Akouto's white label managed cyber security solution provides advanced protection against online threats and security breaches to prevent financial loss caused by viruses and malware, ransomware & extortion, unplanned downtime and data corruption. Our Managed Security service partners are armed with the expertise, technology and personnel needed to defend businesses against constantly changing threats and attacks.
Technology + Expertise
Our solution protects against inbound threats, prevents users from accessing malicious sites and helps identify systems infected by the latest malware able to bypass and hide from anti-virus. Systems are actively monitored using automated analytics and real cybersecurity experts to identify threats and troubleshoot problems.Easy to deploy and manage
Our solution is inserted at the network edge with no configuration changes needed to existing routers or firewalls. The solution is centrally monitored by cybersecurity experts who assess threat information and guide IT personnel to quickly contain and resolve issues to keep your business up and running.Save time and money
Getting security right takes time and expertise. Getting it wrong is easy and can result in costly breaches, ransomware and lost revenue due to unplanned downtime. Our cybersecurity solution and experts solve this problem by taking on the cybercriminals allowing you and your staff to focus on the projects and activities that drive your business.What is Akouto Managed Security?
An Inline Intrusion Prevention Security Appliance
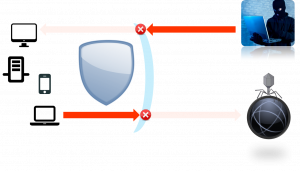
The Network Security appliance blocks inbound threats and prevents users from accessing malicious sites and content. It also helps identify internal systems that are infected with malware that is able to bypass anti-virus.
Advanced Cloud Analytics Algorithms
Advanced algorithms analyse security information to detect hidden issues and alert monitoring staff about any issues that require immediate attention.
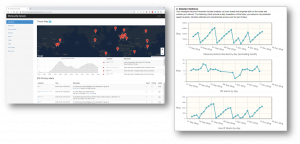
Branded Web Management Portal
Administrator and end-user portals branded with your company logo provide security information, statistics, reports, remote monitoring and management.
A Professionally Monitored Security Service
Security information is streamed to the monitoring servers where trained cybersecurity experts monitor and analyse the information to identify issues and work with your IT staff to contain and mitigate threats.

Cloud Network Scanners
Cloud-based network scanners check customer networks for unauthorized entry points and firewall mis-configurations.
Locate a Distributor:
FEATURES & BENEFITS
Mature industry leading security appliance provides advanced cybersecurity features traditionally only used by large enterprises.
Benefit: Protect your business with Enterprise grade security at a small business price point.
Intrusion Prevention inspects all inbound and outbound traffic to protect against known and emerging cyber security threats.
Benefit: Detect and block malicious activity outside and inside your network.
Advanced firewall rules restrict traffic to and from specific countries, reducing unnecessary exposure to remote threats.
Benefit: Reduce risk by limiting the locations from which your systems can be accessed.
Appliance software versions and patches are actively monitored to ensure your systems are always up to date with the latest security patches and features.
Benefit: Prevent obsolete or vulnerable software and eliminate one of the primary causes of security breaches.
Cloud services and security experts monitor your systems. Automatic SMS and Email alerts enable rapid response to critical security events.
Benefit: Quickly respond to critical issues and threats and minimize the impact of potential security breaches.
Cloud security scanners check external access to your network, protecting it from unauthorized access due to incorrect security policies or configuration errors.
Benefit: Prevent breaches caused by human error and common firewall misconfigurations.
I already have a firewall, why do I need this?
Most firewalls only support very simple policies for securing network traffic and do nothing to prevent computers inside your network from connecting to malicious servers on the internet. When someone is tricked into clicking on a link, your firewall will not stop that computer from connecting to servers controlled by hackers and downloading viruses or other malware disguised as a PDF file or other content.
When you forward ports in your firewall, in most cases those rules apply to everyone on the internet: the same policy that allows your IT administrator remote access through the firewall also gives hackers access to the same ports.
The security sensor includes a mature and robust Intrusion Prevention engine that scans all inbound and outbound traffic for threats. Detailed rules can be created to define what traffic is allowed in and out of your network including restrictions by geographic location. The cloud security scanner regularly scans your network to look for open ports that could provide hackers with unauthorized access.
I already have anti-virus, why do I need this?
Anti-virus is a critical component of a robust cyber security strategy. Unfortunately, while anti-virus solutions prevent many attacks, hackers are constantly adapting their approach in what has become a never ending cat-and-mouse game between anti-virus vendors and cyber-criminals.
Once a hacker is able to trick a user or bypass anti-virus software and install a Trojan or backdoor, they own your network. They remotely control infected systems to explore your network, infect more systems, encrypt your hard drives, steal your business and client information and copy your files to their servers, allowing them full access to your infrastructure. Your antivirus isn’t looking for such activity and does nothing to prevent it.
The security appliance includes advanced Intrusion Prevention capability with rules that are updated regularly by a large community of cyber security professionals. These rules monitor your network traffic for patterns that are known to be associated with specific attacks, blocking the network activity and alerting the cybersecurity team to take the appropriate defensive countermeasures.
Do I need to replace my existing firewall?
If you already have a firewall protecting your network you’ve taken an important step in protecting your infrastructure. You can continue to use your existing firewall that provides basic network security policies along with the enhanced security capabilities that are part of the Akouto solution.
The security appliance can be installed in your network in “transparent mode” either in front of your existing firewall or behind it, significantly enhancing security capabilities with features such as Intrusion Prevention, Geo-IP security policy enforcement, external vulnerability scanning and automated cloud monitoring and alerting.
Do I need both a firewall and the security appliance?
If you don’t already have a firewall, there is no need to buy one. The security appliance provides firewall capabilities that rival standard commercial firewalls and includes many features that are only available in high end (and high price) security appliances.
You can deploy the security appliance in NAT or transparent mode, and leverage all of the capabilities including Firewall, NAT, DHCP, Traffic Shaping, VPN, Intrusion Prevention, High Availability, Load Balancing, SNMP support, DNS Forwarding, Captive Portal and much more.
Do I still need anti-virus?
Yes, you should still use anti-virus on all of your endpoints including desktops, laptops, tablets and mobile phones.
A proper security strategy consists of multiple layers of protection. That includes network layer security as well as endpoint security which is provided by your anti-virus.
The two technologies are complimentary and together provide the best possible protection against different types of vulnerabilities.
I have anti-virus and still got infected, would this have helped?
Akouto's managed security solution provides an additional layer of security that may have been able to detect and stop the attack. It contains thousands of rules that are constantly being updated by an army of cyber-security specialists allowing it to protect your network and systems against a huge number of attacks and vulnerabilities. At the same time, hackers are always finding new ways to bypass security systems. The best strategy is to use a layered approach to security that includes the right mix of technology and human expertise to protect your business.
Who monitors my network security?
Security analytics servers and network scanners continuously collect and analyze data from your security appliances. Critical events that require immediate attention generate SMS and Email alerts sent to the IT security staff managing your infrastructure.
Members of the Akouto cyber security team and your IT service partner monitor your systems through the available security portal to quickly identify and address any issues that may be detected.
How do I know if there is a security incident?
Critical security issues detected by the security analytics servers automatically generate SMS and Email alerts that are sent to the IT security staff managing your infrastructure.
Your IT service partner will notify you of security threats and any countermeasures that should be put in place or actions that should be taken.
What should I do if there is a security incident?
If you suspect there has been a breach or other security incident, you should contact your IT service partner. They are trained to investigate the issue and work with the Akouto cyber security team to identify the threat and take the appropriate action.